我们今天主要介绍,如何使用Curl将linux的数据拷贝到Windows上,其实说到需求,其实有很多办法,比如scp、rsync及mount等工具或方法都可以实现Linux到Windows的数据同步,今天我们主要介绍Curl的数据同步方法,使用Curl的缺陷就是需要在Windows上启用FTP服务,然后配置目录等信息,对于其他的方法,我们会在后面的文章再做介绍,
我们首先在windows上需要启用FTP服务,服务器管理器---添加WEB服务器(IIS)
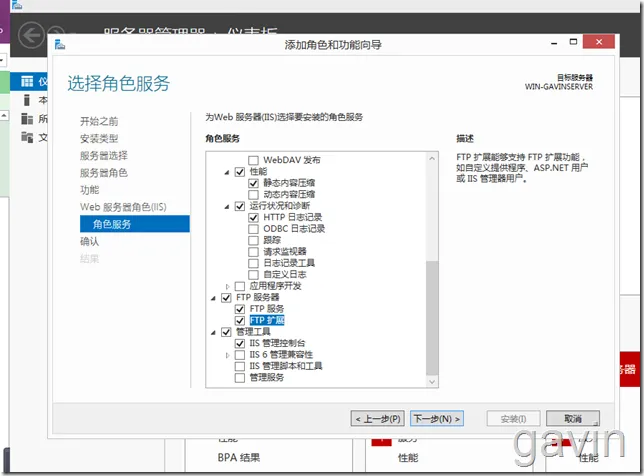
在IIS角色服务中勾选启用FTP服务器等角色
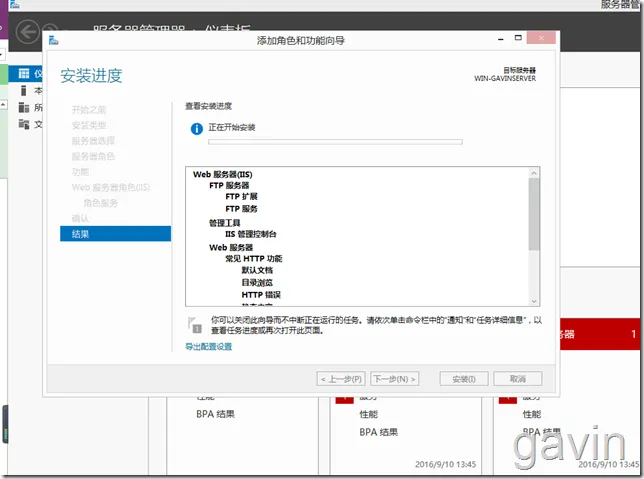
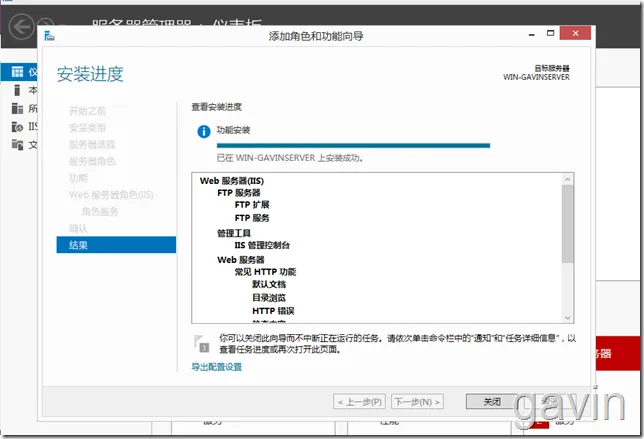
安装完成
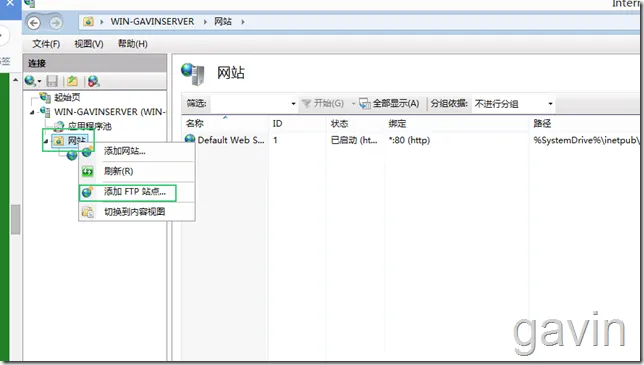
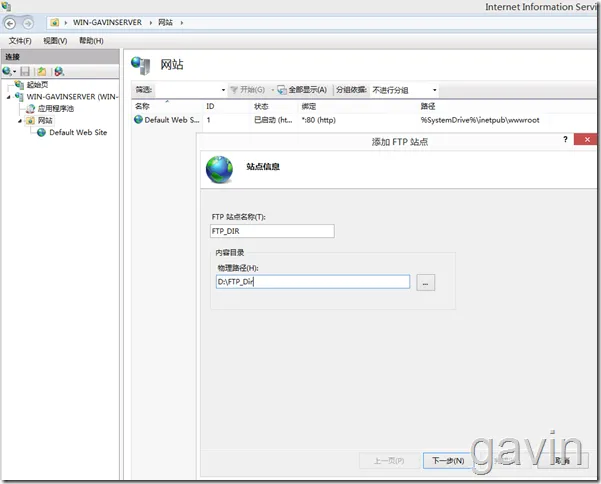
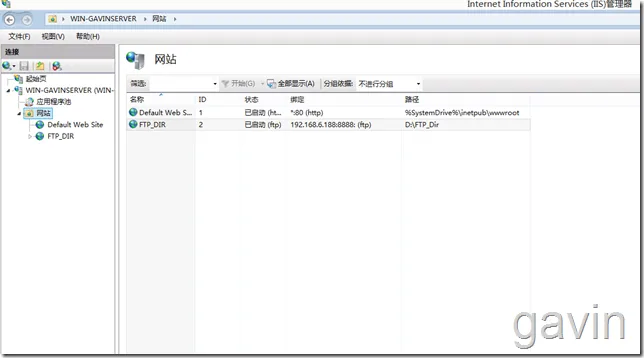
接下来打开IIS管理器;网站---添加FTP站点
配置FTP物理路劲
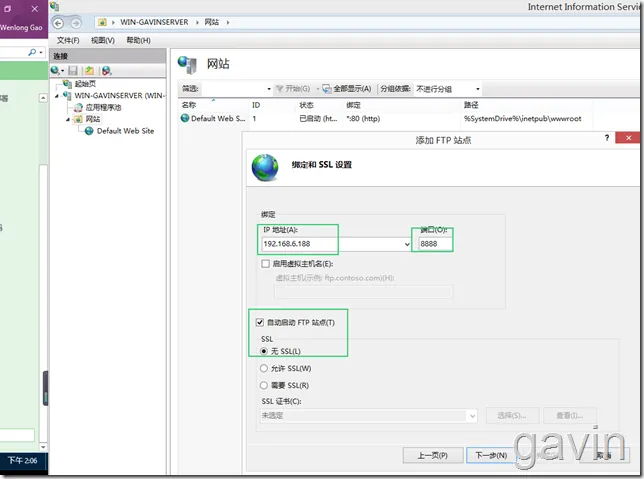
我们配置FTP站点的信息,比如地址及端口信息
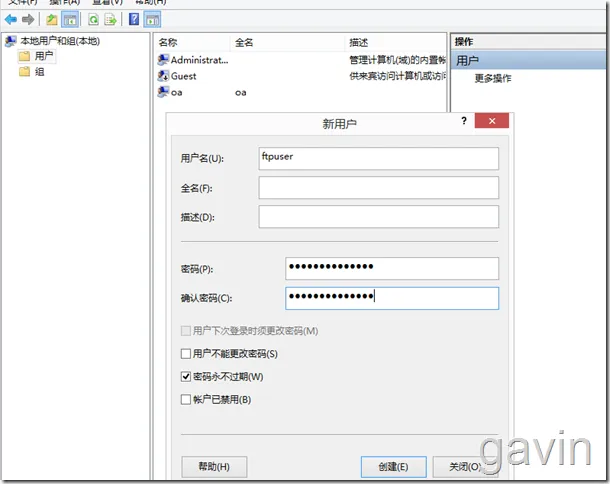
我们创建一个ftpuser用户,主要用来传输文件的认证信息
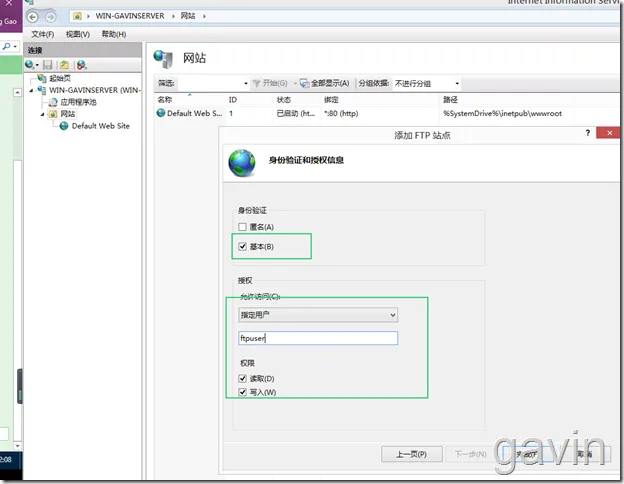
然后配置身份认证方式,选择基本,然后指定用户或用户组都可以,配置权限读写
配置完成
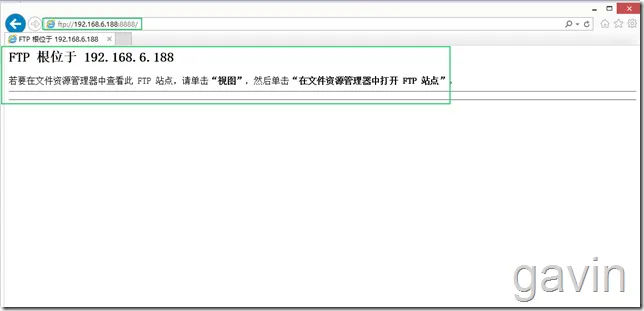
我们通过浏览器访问FTP服务进行测试
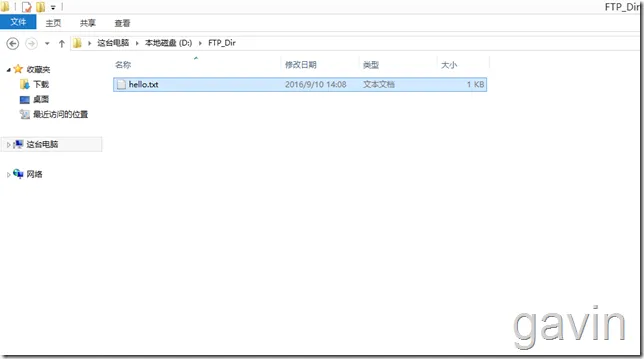
我们在目录下创建一个测试文件
刷新FTP访问可以显示
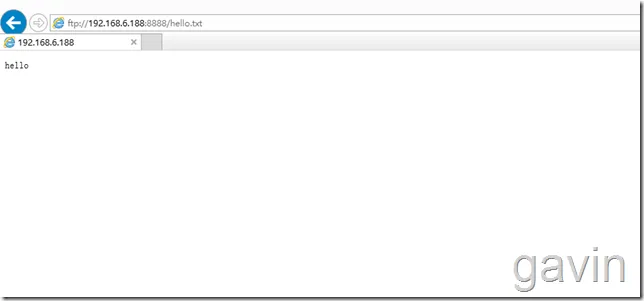
我们也可以打开文件显示
接下来我们要测试将linux上的文件上传到ftp上
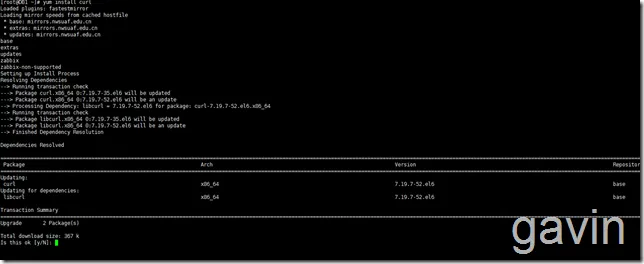
我们首先使用 首先需要在linux安装 curl服务
|
1
|
yum
install
-y curl
|
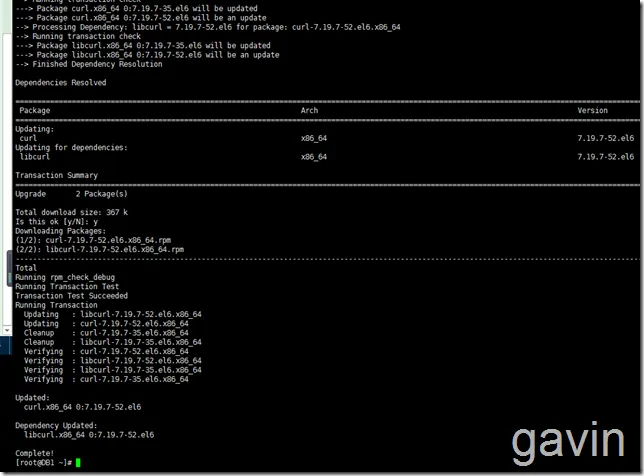
安装后,我们首先查看curl有哪些参数
|
1
|
curl --help
|
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
|
[root@DB1 ~]
# curl --help
Usage: curl [options...] <url>
Options: (H) means HTTP
/HTTPS
only, (F) means FTP only
--anyauth Pick
"any"
authentication method (H)
-a
/--append
Append to target
file
when uploading (F
/SFTP
)
--basic Use HTTP Basic Authentication (H)
--cacert <
file
> CA certificate to verify peer against (SSL)
--capath <directory> CA directory to verify peer against (SSL)
-E
/--cert
<cert[:
passwd
]> Client certificate
file
and password (SSL)
--cert-
type
<
type
> Certificate
file
type
(DER
/PEM/ENG
) (SSL)
--ciphers <list> SSL ciphers to use (SSL)
--compressed Request compressed response (using deflate or
gzip
)
-K
/--config
<
file
> Specify
which
config
file
to
read
--connect-timeout <seconds> Maximum
time
allowed
for
connection
-C
/--continue-at
<offset> Resumed transfer offset
-b
/--cookie
<name=string
/file
> Cookie string or
file
to
read
cookies from (H)
-c
/--cookie-jar
<
file
> Write cookies to this
file
after operation (H)
--create-
dirs
Create necessary
local
directory hierarchy
--crlf Convert LF to CRLF
in
upload
--crlfile <
file
> Get a CRL list
in
PEM
format
from the given
file
-d
/--data
<data> HTTP POST data (H)
--data-ascii <data> HTTP POST ASCII data (H)
--data-binary <data> HTTP POST binary data (H)
--data-urlencode <name=data
/name
@filename> HTTP POST data url encoded (H)
--delegation STRING GSS-API delegation permission
--digest Use HTTP Digest Authentication (H)
--disable-eprt Inhibit using EPRT or LPRT (F)
--disable-epsv Inhibit using EPSV (F)
-D
/--dump-header
<
file
> Write the headers to this
file
--egd-
file
<
file
> EGD socket path
for
random data (SSL)
--engine <eng> Crypto engine to use (SSL).
"--engine list"
for
list
-f
/--fail
Fail silently (no output at all) on HTTP errors (H)
-F
/--form
<name=content> Specify HTTP multipart POST data (H)
--form-string <name=string> Specify HTTP multipart POST data (H)
--
ftp
-account <data> Account data to send when requested by server (F)
--
ftp
-alternative-to-user <cmd> String to replace
"USER [name]"
(F)
--
ftp
-create-
dirs
Create the remote
dirs
if
not present (F)
--
ftp
-method [multicwd
/nocwd/singlecwd
] Control CWD usage (F)
--
ftp
-pasv Use PASV
/EPSV
instead of PORT (F)
-P
/--ftp-port
<address> Use PORT with address instead of PASV (F)
--
ftp
-skip-pasv-ip Skip the IP address
for
PASV (F)
--
ftp
-ssl Try SSL
/TLS
for
ftp
transfer (F)
--
ftp
-ssl-ccc Send CCC after authenticating (F)
--
ftp
-ssl-ccc-mode [active
/passive
] Set CCC mode (F)
--
ftp
-ssl-control Require SSL
/TLS
for
ftp
login,
clear
for
transfer (F)
--
ftp
-ssl-reqd Require SSL
/TLS
for
ftp
transfer (F)
-G
/--get
Send the -d data with a HTTP GET (H)
-g
/--globoff
Disable URL sequences and ranges using {} and []
-H
/--header
<line> Custom header to pass to server (H)
-I
/--head
Show document info only
-h
/--help
This help text
--hostpubmd5 <md5> Hex encoded MD5 string of the host public key. (SSH)
-0
/--http1
.0 Use HTTP 1.0 (H)
--ignore-content-length Ignore the HTTP Content-Length header
-i
/--include
Include protocol headers
in
the output (H
/F
)
-k
/--insecure
Allow connections to SSL sites without certs (H)
--interface <interface> Specify network interface
/address
to use
-4
/--ipv4
Resolve name to IPv4 address
-6
/--ipv6
Resolve name to IPv6 address
-j
/--junk-session-cookies
Ignore session cookies
read
from
file
(H)
--keepalive-
time
<seconds> Interval between keepalive probes
--key <key> Private key
file
name (SSL
/SSH
)
--key-
type
<
type
> Private key
file
type
(DER
/PEM/ENG
) (SSL)
--krb <level> Enable Kerberos with specified security level (F)
--libcurl <
file
> Dump libcurl equivalent code of this
command
line
--limit-rate <rate> Limit transfer speed to this rate
-l
/--list-only
List only names of an FTP directory (F)
--
local
-port <num>[-num] Force use of these
local
port numbers
-L
/--location
Follow Location: hints (H)
--location-trusted Follow Location: and send auth to other hosts (H)
-M
/--manual
Display the full manual
--max-filesize <bytes> Maximum
file
size to download (H
/F
)
--max-redirs <num> Maximum number of redirects allowed (H)
-m
/--max-time
<seconds> Maximum
time
allowed
for
the transfer
--negotiate Use HTTP Negotiate Authentication (H)
-n
/--netrc
Must
read
.netrc
for
user name and password
--netrc-optional Use either .netrc or URL; overrides -n
-N
/--no-buffer
Disable buffering of the output stream
--no-keepalive Disable keepalive use on the connection
--no-sessionid Disable SSL session-ID reusing (SSL)
--noproxy Comma-separated list of hosts
which
do
not use proxy
--ntlm Use HTTP NTLM authentication (H)
-o
/--output
<
file
> Write output to <
file
> instead of stdout
--pass <pass> Pass phrase
for
the private key (SSL
/SSH
)
--post301 Do not switch to GET after following a 301 redirect (H)
--post302 Do not switch to GET after following a 302 redirect (H)
-
#/--progress-bar Display transfer progress as a progress bar
-x
/--proxy
<host[:port]> Use HTTP proxy on given port
--proxy-anyauth Pick
"any"
proxy authentication method (H)
--proxy-basic Use Basic authentication on the proxy (H)
--proxy-digest Use Digest authentication on the proxy (H)
--proxy-negotiate Use Negotiate authentication on the proxy (H)
--proxy-ntlm Use NTLM authentication on the proxy (H)
-U
/--proxy-user
<user[:password]> Set proxy user and password
--proxy1.0 <host[:port]> Use HTTP
/1
.0 proxy on given port
-p
/--proxytunnel
Operate through a HTTP proxy tunnel (using CONNECT)
--pubkey <key> Public key
file
name (SSH)
-Q
/--quote
<cmd> Send
command
(s) to server before
file
transfer (F
/SFTP
)
--random-
file
<
file
> File
for
reading random data from (SSL)
-r
/--range
<range> Retrieve only the bytes within a range
--raw Pass HTTP
"raw"
, without any transfer decoding (H)
-e
/--referer
Referer URL (H)
-O
/--remote-name
Write output to a
file
named as the remote
file
--remote-name-all Use the remote
file
name
for
all URLs
-R
/--remote-time
Set the remote
file
's
time
on the
local
output
-X
/--request
<
command
> Specify request
command
to use
--retry <num> Retry request <num>
times
if
transient problems occur
--retry-delay <seconds> When retrying, wait this many seconds between each
--retry-max-
time
<seconds> Retry only within this period
-S
/--show-error
Show error. With -s,
make
curl show errors when they occur
-s
/--silent
Silent mode. Don't output anything
--socks4 <host[:port]> SOCKS4 proxy on given host + port
--socks4a <host[:port]> SOCKS4a proxy on given host + port
--socks5 <host[:port]> SOCKS5 proxy on given host + port
--socks5-
hostname
<host[:port]> SOCKS5 proxy, pass host name to proxy
--socks5-gssapi-service <name> SOCKS5 proxy service name
for
gssapi
--socks5-gssapi-nec Compatibility with NEC SOCKS5 server
-Y
/--speed-limit
Stop transfer
if
below speed-limit
for
'speed-time'
secs
-y
/--speed-time
Time needed to trig speed-limit abort. Defaults to 30
-2
/--sslv2
Use SSLv2 (SSL)
-3
/--sslv3
Use SSLv3 (SSL)
--stderr <
file
> Where to redirect stderr. - means stdout
--tcp-nodelay Use the TCP_NODELAY option
-t
/--telnet-option
<OPT=val> Set telnet option
-z
/--time-cond
<
time
> Transfer based on a
time
condition
-1
/--tlsv1
Use => TLSv1 (SSL)
--tlsv1.0 Use TLSv1.0 (SSL)
--tlsv1.1 Use TLSv1.1 (SSL)
--tlsv1.2 Use TLSv1.2 (SSL)
--trace <
file
> Write a debug trace to the given
file
--trace-ascii <
file
> Like --trace but without the hex output
--trace-
time
Add
time
stamps to trace
/verbose
output
-T
/--upload-file
<
file
> Transfer <
file
> to remote site
--url <URL> Set URL to work with
-B
/--use-ascii
Use ASCII
/text
transfer
-u
/--user
<user[:password]> Set server user and password
-A
/--user-agent
<string> User-Agent to send to server (H)
-
v
/--verbose
Make the operation
more
talkative
-V
/--version
Show version number and quit
-w
/--write-out
<
format
> What to output after completion
-q
|
翻译过来我们经常会使用一下上传
|
1
2
3
|
-
#/--progress-bar 进度条显示当前的传送状态
-T
/--upload-file
<
file
> 上传文件
-O/—download
file
下载文件
|
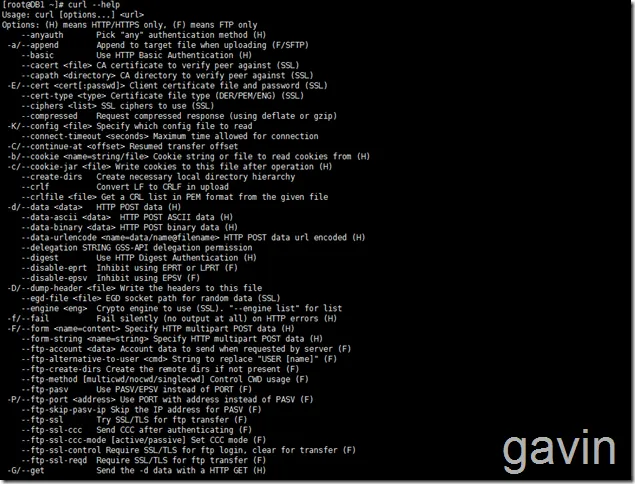
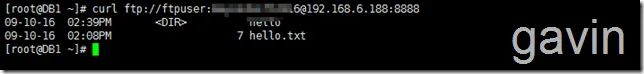
我们先使用curl命令列表ftp服务器上的目录列表
|
1
2
|
crul
ftp
:
//192
.168.6.188:8888/ --user ftpuser:ftpuserpassword
crul
ftp
:
//192
.168.6.188:8888/ -u ftpuser:ftpuserpassword
|
|
1
|
curl
ftp
:
//ftpuser
:ftpuserpassword@192.168.6.188:8888
|
|
1
2
3
4
|
我们下载一个文件
curl
ftp
:
//192
.168.6.188:8888
/hello
.txt -u ftpuser:ftpuserpwd2016 -o hello.txt
或者命令
curl -u ftpuser:ftppass -O
ftp
:
//192
.168.6.188:8888
/hello
.txt
|
|
1
2
3
4
5
6
7
|
如果需要下载全部文件:
curl -u ftpuser:ftppass -Oftp:
//192
.168.6.188:8888/
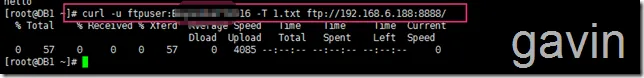
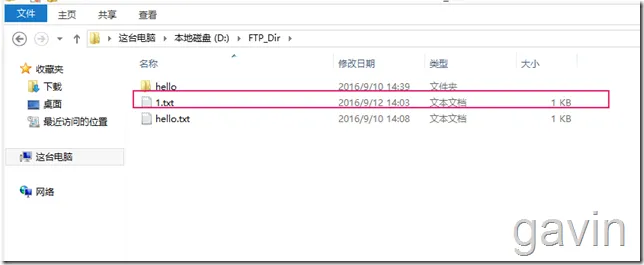
最后我们尝试上传一个文件
curl -u ftpuser:ftpuserpwd -T 1.txt
ftp
:
//192
.168.6.188:8888/
如果需要上传多个文件
curl -u ftpuser:ftppass -T
"{file1,file2}"
ftp
:
//192
.168.6.188:8888/
|
因为我们要定期自动上传,所以,我们需要将该命令编写成一个shell脚本;最简单的方法是
|
1
2
3
4
5
6
|
#!/bin/bash
user=”ftpuser”
pwd
=”ftpuserpwd”
#curl -u ftpuser::ftpuserpwd -T 1.txt ftp://192.168.6.188:8888/
curl –u $user$
pwd
-T 1.txt
ftp
:
//192
.168.6.188:8888/
exit
|
然后我们可以使用crontal -e进行编辑计划任务
|
1
2
|
30 23 * * * shell路劲 每天23点30执行脚本
23 23 * * *
/root/uploadfile
.sh
|
本文转自 高文龙 51CTO博客,原文链接:http://blog.51cto.com/gaowenlong/1856299,如需转载请自行联系原作者

![clip_image001[3] clip_image001[3]](https://ucc.alicdn.com/grng7az2sxifq/developer-article428037/20241018/76207b89403346a5a3ace97b46191cf1.png?x-oss-process=image/resize,w_1400/format,webp)