TH_GREP report is vulnerable for command execution vulnerability which is working with previous patch (note 1433101). Remote OS command execution is possible
Application: SAP NetWeaver
Versions Affected: SAP NetWeaver
Vendor URL: http://www.SAP.com
Bugs: Command execution
Reported: 08.04.2011
Vendor response: 09.04.2011
Date of Public Advisory: 11.11.2011
CVSS: 6.0
CVE-number:
Author: Alexey Tyurin from DSecRG (research center of ERPScan)
Description
***********
TH_GREP report is vulnerable for command execution vulnerability which is working with previous patch (note 1433101). Remote OS command execution is possible
Details
*******
This vulnerability exists in patched version (note 1433101) because this note secure only linux but we found that windows is vulnerable too.
There is ability for command execution via SA "TH_GREP" RFC-function in OS Windows.
The problem contains in user input validation absence of "TH_GREP" RFC-function's parameters. An attacker can insert malicious code in "<STRING>"-parameter for command execution.
There are minimum 3 ways of command execution and attacker must have valid credentials:
1) In transaction "Se37"
2) via "startrfc" command with "TH_GREP" RFC-function
3) via a crafted "TH_GREP" RFC-SOAP-request
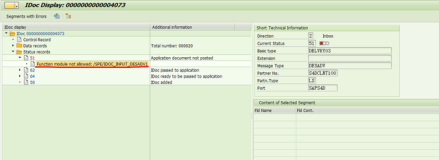
Example:
******
Working exploit is available in commercial scanner ERPScan Security Scanner for SAP (http://erpscan.com)
References
**********
http://dsecrg.com/pages/vul/show.php?id=339
http://www.sdn.sap.com/irj/sdn/index?rid=/webcontent/uuid/c05604f6-4eb3-2d10-eea7-ceb666083a6a
https://service.sap.com/sap/support/notes/1580017
Fix Information
*************
Solution to this issue is given in the SAP Security Note 1580017.
About DSecRG
*******
The main mission of DSecRG is to conduct researches of business critical systems such as ERP, CRM, SRM, BI, SCADA, banking software and others. The result of this work is then integrates in ERPScan Security Scanner. Being on the top edge of ERP and SAP security DSecRG research helps to improve a quality of ERPScan consulting services and protects you from the latest threads.
Contact: research [at] dsecrg [dot] com
http://www.dsecrg.com
About ERPScan
*******
ERPScan is an innovative company engaged in the research of ERP security and develops products for ERP system security assessment. Apart from this the company renders consulting services for secure configuration, development and implementation of ERP systems, and conducts comprehensive assessments and penetration testing of custom solutions.
Our flagship products are "ERPScan Security Scanner for SAP" and service "ERPScan Online" which can help customers to perform automated security assessments and compliance checks for SAP solutions.
Contact: info [at] erpscan [dot] com
http://www.erpscan.com